
One Monday morning, the security team gathered for their regular risk review meeting. The risk register was open on the...
This site documents my progression from learner to human-centered cybersecurity

One Monday morning, the security team gathered for their regular risk review meeting. The risk register was open on the...

Every year, the cybersecurity industry faces a growing problem: there are millions of unfilled jobs worldwide, yet many talented women...
When people hear the word cybersecurity, they often imagine technical teams working behind the scenes installing firewalls, monitoring systems, and...
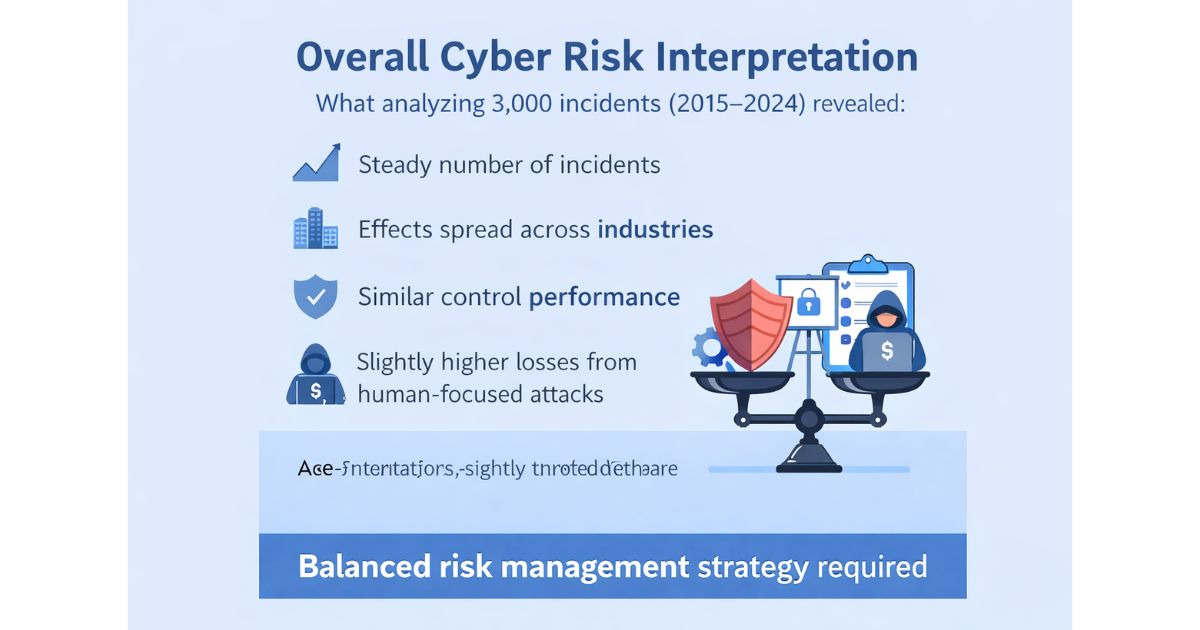
Cyber risk is often discussed in headlines rising attacks, record-breaking breaches, increasing losses. But what does the data actually say?...
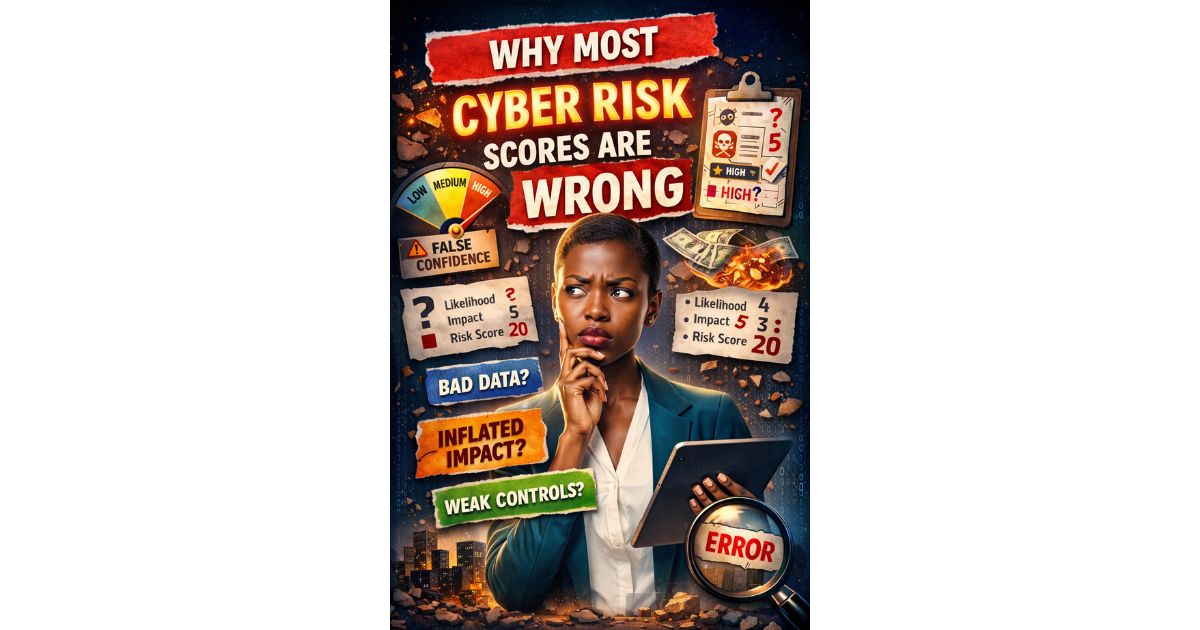
Most cyber risk registers look structured. They have: On paper, it appears disciplined. But in practice, many of those scores...

The risk was documented. It had a score.It had a description.It even had recommended controls. But no one owned it....