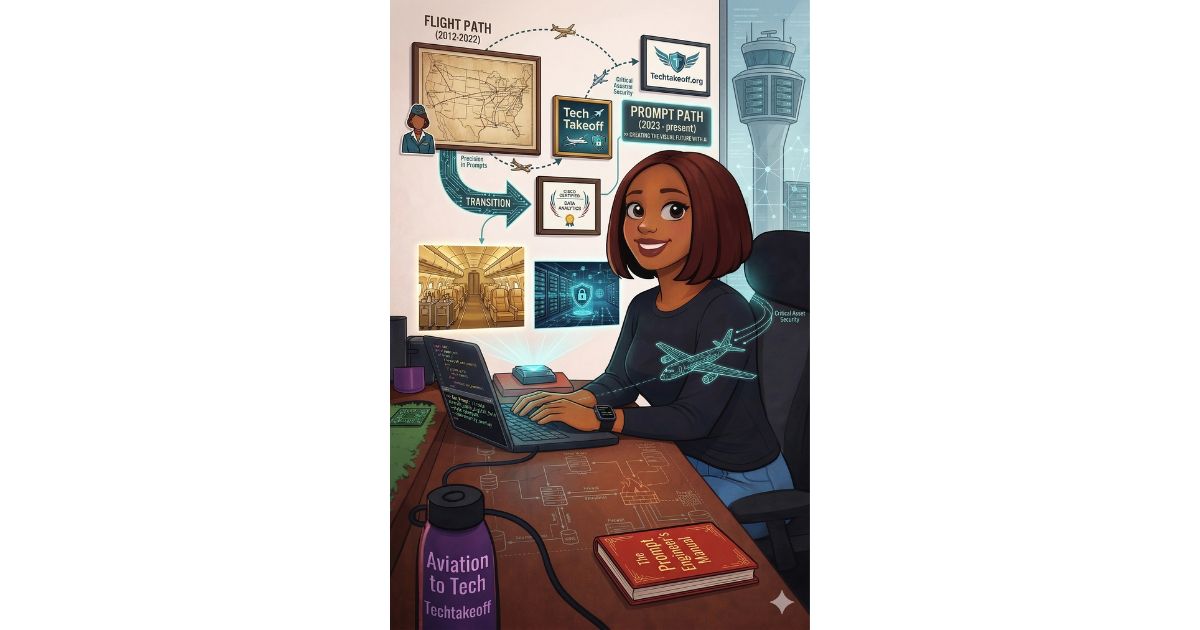
When I started my transition from aviation to cybersecurity, I knew I wanted Techtakeoff to have a unique visual identity. I didn’t want generic stock photos; I wanted images that reflected my journey, my style, and the future I am building. That’s when I stepped into the world of Prompt Engineering. I did a course in AI for creatives. What is an AI Prompt? Think of an AI prompt like a flight plan. Just as a pilot needs specific coordinates, weather data, and altitude instructions to reach a destination, an AI model needs descriptive text to land on the right image. My Creative Process To create the visuals you see on this blog, I use Text-to-Image generative tools. I don’t just type “girl at a laptop.” I have to be the director, the lighting technician, and the stylist. For example, to create my “Tech Branding” images, I use detailed prompts like: A high-quality 3D animation style illustration of a confident Black woman with a sleek bob and glasses, sitting at a modern outdoor cafe. she is writing in a notebook labeled ‘Techtakeoff,’ with a laptop and coffee nearby. Cinematic lighting, soft morning sun, professional and chic aesthetic. Why This Matters for My Tech Journey You might wonder: What does making art have to do with Cybersecurity? The answer is Precision.
Why Cybersecurity Is a Business Problem, Not Just an IT Problem
When people hear the word cybersecurity, they often imagine technical teams working behind the scenes installing firewalls, monitoring systems, and defending networks from hackers. Because of this, many assume cybersecurity is simply an IT responsibility. But the reality is different. Cybersecurity is not just a technical issue. It is a business risk issue that affects operations, finances, reputation, and customer trust. When a cyber incident happens, the consequences extend far beyond the IT department. Understanding cybersecurity as a business problem helps organisations make better decisions about risk, resources, and long-term resilience. Cyber Incidents Can Disrupt Business Operations One of the most immediate effects of a cyber attack is operational disruption. When critical systems are compromised or unavailable, normal business activities can come to a halt. For example, ransomware attacks often lock organisations out of their own systems, making it impossible to access files, process transactions, or communicate internally. In some cases, companies cannot deliver services to customers or run essential operations until systems are restored. This is why cybersecurity is closely tied to business continuity. When systems fail, the impact is felt across the entire organisation not just in the IT department. Financial Loss Is a Real Risk Cyber incidents can also lead to significant financial consequences. Organisations may face costs such as: Even when systems are restored quickly, the financial impact can be substantial. For many organisations, cybersecurity failures are not just technical problems they become financial risks that leadership must manage. Customer Trust Can Be Damaged Modern businesses rely heavily on customer trust, especially when handling personal data, financial information, or digital services. If a cyber incident exposes customer data or disrupts services, customers may begin to question whether the company can protect their information. Rebuilding trust after a major security incident can take years. In some cases, customers simply move to competitors they believe are more secure. This is why cybersecurity is closely connected to brand reputation and customer confidence. Regulatory Consequences Can Follow Many industries are now subject to data protection and cybersecurity regulations. When organisations fail to protect sensitive data, regulators may investigate and impose penalties. These consequences can include fines, legal obligations, or increased oversight. For leadership teams, this means cybersecurity risks must be managed not only from a technical perspective but also from a compliance and governance perspective. Cybersecurity Requires Business-Level Decisions Because cybersecurity affects operations, finances, reputation, and compliance, it cannot be managed by technical teams alone. Effective cybersecurity requires business-level decision making, including: These decisions often involve senior leadership, risk managers, legal teams, and operational leaders not just IT specialists. Security Teams and Business Leaders Must Work Together Cybersecurity works best when technical teams and business leaders collaborate. Security professionals can identify threats and recommend controls, but leadership must decide how risks align with the organisation’s risk appetite, priorities, and resources. When cybersecurity is treated purely as an IT issue, organisations may underestimate the broader consequences of cyber incidents. When it is treated as a business risk, security becomes part of strategic decision-making. On a final note…. Cybersecurity is often associated with technical tools and defensive technologies. However, the real impact of cyber incidents is felt across the entire organisation. System disruptions, financial losses, regulatory exposure, and damage to customer trust all make cybersecurity a business problem, not just a technical one. Organisations that understand this shift are better prepared to manage cyber risk, protect their operations, and maintain trust with customers. In the end, cybersecurity is not only about defending networks it is about protecting the business itself.
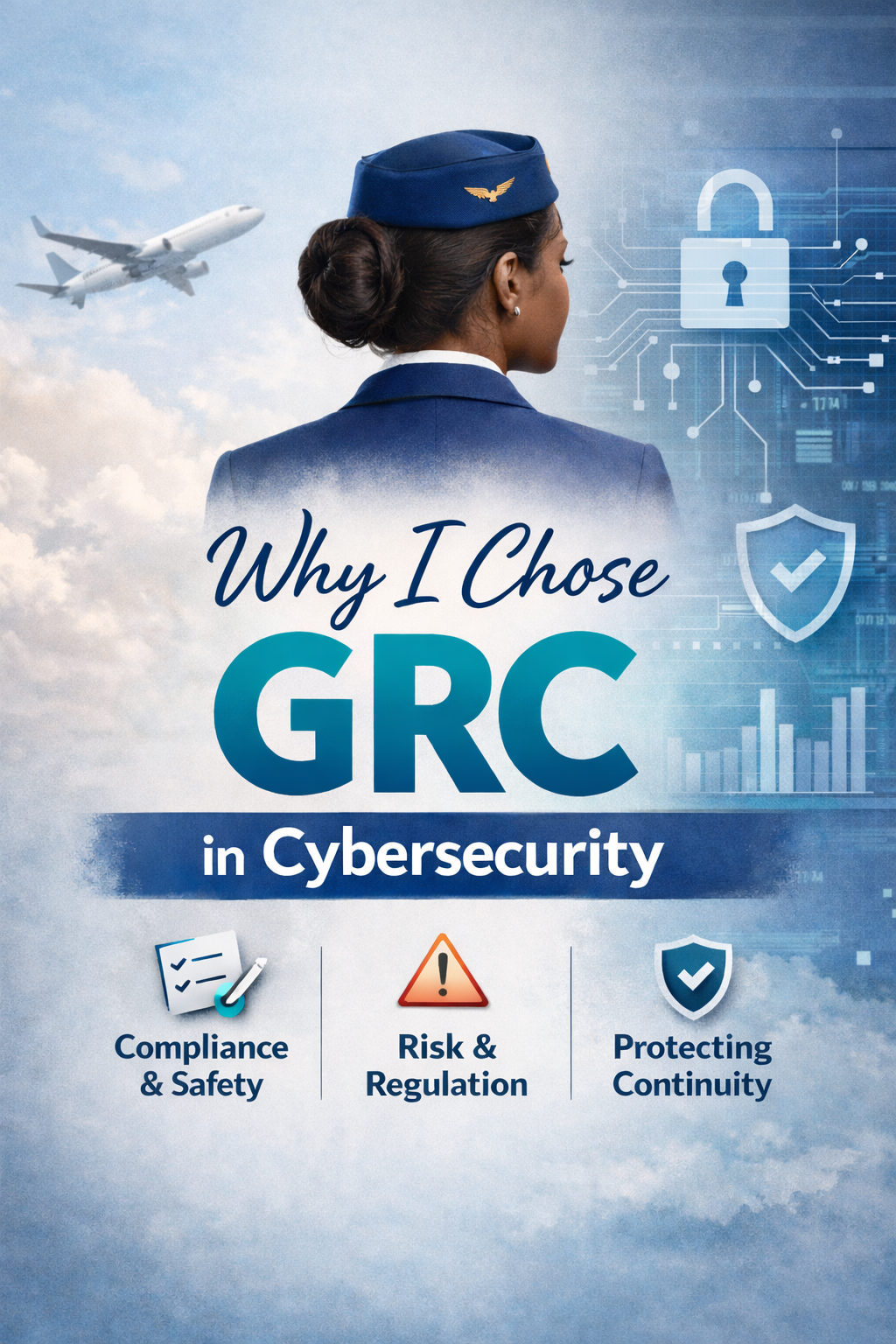
What Aviation Taught Me About GRC (And Why Cybersecurity Needs It)
Amara didn’t miss a step because she didn’t care. She missed it because it was early, she was tired, and several things were happening at the same time. None of them felt serious on their own but that is usually how problems begin. In aviation, we expect moments like this.That’s why we have procedures. Not to control people, but to support them. That mindset is what first made Governance, Risk, and Compliance (GRC) feel familiar to me when I started learning cybersecurity. Aviation Runs on Governance Even If It Doesn’t Call It That In aviation, there is one clear goal: safe and reliable operations. Everything supports that goal: This is governance in action. What aviation calls “procedures” is really a way of making sure everyone knows: The structure exists to help the business run safely and consistently. That is exactly what good GRC is meant to do in cybersecurity. GRC Is Not the Problem Poorly Designed GRC Is When people complain about cybersecurity policies, they are often not reacting to GRC itself. They are reacting to: Good GRC is different. Good GRC connects security to business goals.It explains why controls exist and how they support the organisation. Just like aviation procedures support safety, trust, and continuity. Lesson One: Checklists Support People Under Pressure In aviation, even very experienced crew members use checklists. Not because they don’t know their jobs.But because pressure, fatigue, and distraction affect everyone. Checklists are there to make sure important steps are not missed when things get busy. In cybersecurity, GRC plays this role. Policies, procedures, and playbooks turn complex risks into clear actions.They help people do the right thing at the right time. This is not bureaucracy.This is risk management in practice. Lesson Two: Structure Helps the Business Move Faster Aviation is highly structured, but it is not slow. Because everyone knows: Decisions are made quickly and calmly, even in difficult situations. In cybersecurity, structure works the same way. Clear governance: Structure does not block the business.It protects it. Lesson Three: Reporting Without Fear Strengthens Risk Management Aviation encourages people to report mistakes and near-misses. The goal is not punishment.The goal is learning and prevention. This is strong risk management. In cybersecurity, GRC helps create the same environment. When people feel safe to report issues: Risk cannot be managed if it is hidden. From Blame to Better Design People will always make mistakes. Good systems are designed with that in mind. Aviation does not rely on perfect people.It relies on well-designed governance. Cybersecurity is no different. GRC is how organisations design security that works with people, not against them. Why This Matters for Cybersecurity Today Cybersecurity is becoming more complex. More systems.More data.More pressure on individuals. Without strong GRC, security becomes reactive and confusing. With good GRC: This is how cybersecurity becomes sustainable. Why GRC Makes Sense to Me Coming from aviation, GRC feels natural. Both industries deal with risk, trust, and responsibility.Both rely on clear rules to support complex operations. GRC is not about slowing things down.It is about helping organisations operate safely, confidently, and consistently. Security is not about perfect people. It is about clear governance, smart risk management, and systems that support the business when things are under pressure. That is the kind of cybersecurity I believe in.
Structure Is a Security Skill
When people think about cybersecurity, they often imagine firewalls, tools, and complex systems. But one of the most underrated security skills is not technical at all. It is structure. Structure is what keeps things from falling apart when humans get tired, rushed, or distracted. And since humans are always part of the system, structure becomes a form of protection. In security and GRC, structure shows up as policies, procedures, playbooks, and clear roles. Not because people don’t care but because caring alone is not enough. When there is no structure, decisions are made on the fly. And decisions made under pressure are where most security incidents begin. Structure removes guesswork. It tells people: Without structure, security relies on memory, good intentions, and “common sense.” And those fail when urgency, fear, or convenience enters the picture. Think about incident response. When something goes wrong, the goal is not to panic it is to follow a plan. That plan exists so people don’t have to think under stress. They just act. That is structure doing its job. Structure is also what turns awareness into action. Training tells people what could happen. Structure tells them what to do when it does. This is why GRC values documentation, reviews, and consistency. It is not paperwork for the sake of paperwork. It is a safety net. A way to protect people from their own limits. Strong security systems don’t expect humans to be perfect.They expect humans to be human and they build structure around that reality. Because in cybersecurity, structure doesn’t slow you down.It keeps you safe when it matters most. And that is why structure is not boring.It’s a skill.A security skill.
Why I Chose GRC in Cybersecurity
When I first decided to move into cybersecurity, I didn’t know how wide the field really was. To me, cybersecurity was just… cybersecurity. I didn’t yet understand that it had many different roles, paths, and specialisations. That clarity only started to come after training. During my cybersecurity training, I was exposed to different areas, but I still hadn’t made a decision. I was learning, observing, and trying to understand where I fit. The Internship That Helped Me Be Honest With Myself I got an opportunity to intern remotely at a cybersecurity company for one month. During that time, we were taught more about penetration testing and report writing. And this is where something important happened. I was bored. Not because the work wasn’t important but because it didn’t spark anything in me. I paid attention to how I felt and chose to be honest with myself. I realised that this side of cybersecurity didn’t excite me, and pretending otherwise wouldn’t help my journey. That honesty mattered. Discovering Cyber Threat Intelligence Later on, I took a course in Cisco Cyber Threat Intelligence. This experience felt completely different. I loved it. It sparked my curiosity. I enjoyed understanding threats, patterns, behaviours, and why attacks happen not just how they happen. For the first time, I felt engaged instead of forcing interest. That curiosity pushed me further. The Moment I Found GRC I started watching more videos on YouTube, especially content related to risk management. That was when I came across GRC; Governance, Risk, and Compliance. Something clicked. I found myself drawn to this side of cybersecurity and couldn’t immediately explain why. So I asked myself a simple question: Why am I drawn to GRC? Connecting the Dots With My Work Experience Out of curiosity, I typed that exact question into ChatGPT. I explained my background, that I had been a flight attendant for over a decade. The response stopped me in my tracks. I was told that I was likely drawn to GRC because compliance, regulations, procedures, and safety rules had been part of my life for years. And that was true. As a flight attendant, compliance wasn’t optional. Regulations had to be followed. Procedures existed for a reason. Safety depended on structure, accountability, and consistency. I wasn’t starting something new.I was recognising something familiar. Why GRC Makes Sense for Me GRC focuses on: It’s about understanding what could go wrong, how to reduce the impact, and how to respond when things don’t go as planned. That mindset felt natural to me. On A Final note…. Choosing GRC wasn’t about chasing a title or forcing a role.It was about paying attention to my interests, my curiosity, and my past work experience. Cybersecurity is a big field.Finding your place in it starts with honesty. For me, GRC didn’t feel foreign.It felt like home just in a different industry.
Why Convenience Is The Enemy Of Security
In the beginning, convenience felt harmless. When I first started using social media, I didn’t think much about passwords. I wasn’t careless I was being practical. Using the same password for all my accounts made life easier. One password to remember. No stress. No confusion. It felt efficient. And honestly, I thought, “At least I won’t forget it.” What I didn’t understand then was that convenience quietly trades comfort for risk. When Convenience Feels Smart….Until It Isn’t Using one password everywhere worked… until it didn’t. When my Google account was taken over, the process of getting it back was long and exhausting. Emails. Verifications. Waiting. Proving ownership again and again. It took time, patience, and persistence before I finally recovered it. That experience alone was sobering. But when my Facebook page was taken over, I made a different decision. I didn’t fight for it the same way. I simply started again and built a new one from scratch. Not because it didn’t matter but because the cost of recovery felt heavier than starting over. Both experiences taught me something I had ignored before. Convenience Creates Single Points of Failure The problem with convenience is not that it is wrong it is that it concentrates risk. One password across multiple platforms means one mistake opens many doors. Once that password is exposed, everything connected to it becomes vulnerable. I didn’t fully understand this until I lived through the recovery process. It was during that time resetting access, securing accounts, rebuilding that the importance of passwords finally became clear to me. Security Is Designed to Be Inconvenient for a Reason Security slows you down on purpose. Multiple passwords.Verification steps.Authentication codes. All of these things feel inconvenient because they interrupt ease. But that interruption is intentional. It exists to protect you during moments when convenience would otherwise cost you everything. Attackers depend on ease.Security depends on friction. And most people are not patient, we are always in a hurry. What Changed for Me After those experiences, I stopped prioritising convenience over protection. I began to see passwords not as obstacles, but as boundaries. I understood that the slight discomfort of managing them properly was nothing compared to the stress of losing access and control over my digital life. Convenience had taught me comfort.Security taught me responsibility. Final Thought Convenience feels good in the moment.Security protects you in the long run. Most security failures don’t happen because people are reckless they happen because people choose what feels easiest. And sometimes, the easiest choice is the most expensive one. Want more like this?I write about human-centred cybersecurity, risk, and career transitions.
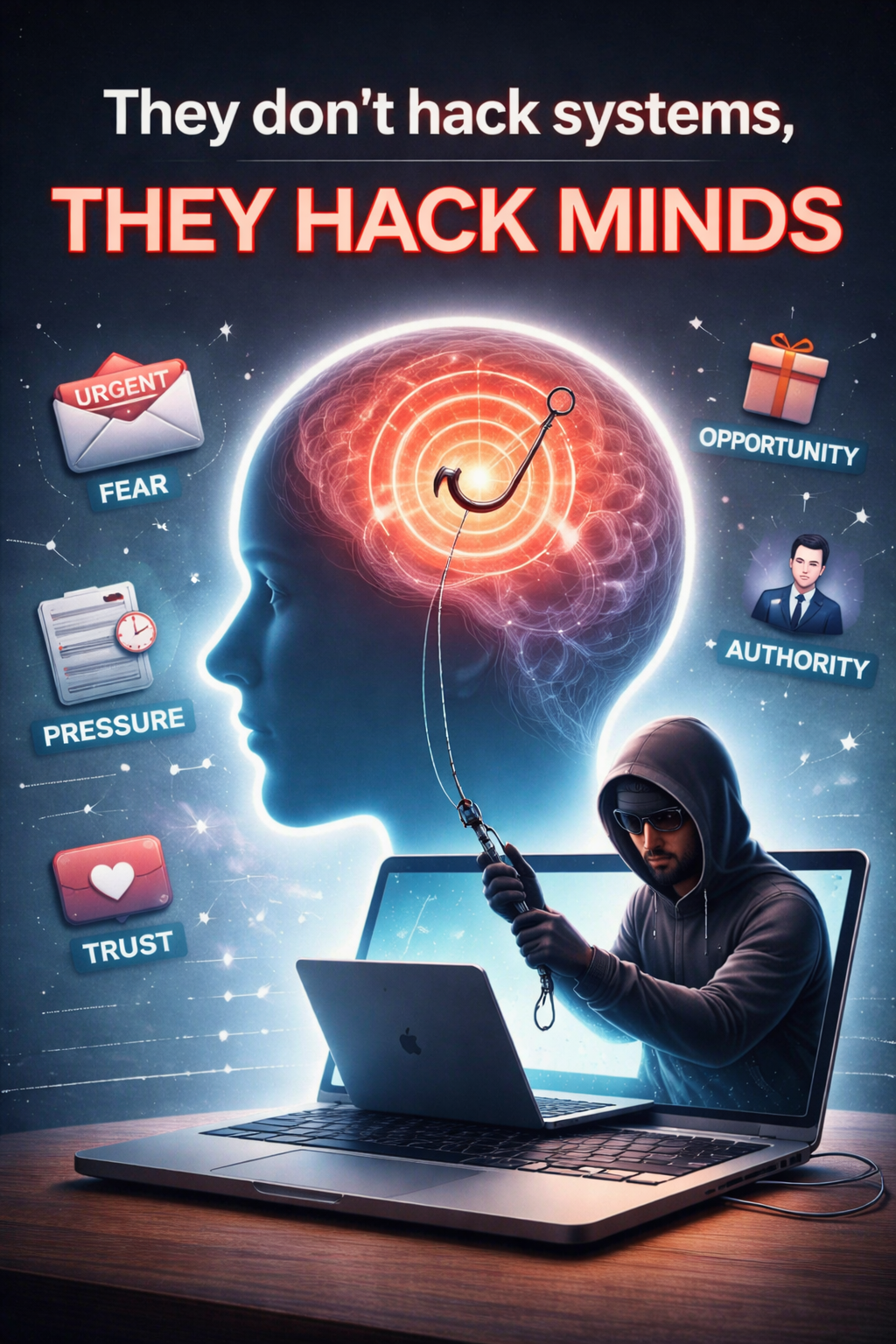
Why Attackers Don’t Hack Systems,They Hack People Instead.
Before attackers go after systems, networks, or software, they go after something far more powerful: the human mind. That’s where the real game is played. As human beings, we are wired in very specific ways. We trust. We help. We respond quickly to urgency. We don’t want to miss opportunities. We don’t want to get into trouble. These traits help society functionbut they also make us vulnerable. Attackers understand this better than most people realize. They don’t need to break technology if they can influence behaviour.And influencing behaviour starts in the mind. The Mind Is the First Attack Surface Cyberattacks don’t begin with code.They begin with emotions. Fear.Pressure.Excitement.Authority.Opportunity. Once an attacker triggers any of these, critical thinking often slows down. Logic steps aside, and reaction takes over. At that point, the hardest part of the attack is already done. Systems Are Built to Resist ,Humans Are Built to Trust Modern systems are designed with layers of protection: passwords, firewalls, encryption, and access controls. Breaking through them directly takes time, skill, and effort. Humans, on the other hand, are not built to resist they are built to connect. We assume good intent.We respond when something sounds important.We act quickly when consequences are mentioned. Attackers exploit this difference. So instead of fighting the system, they go around it by targeting the person using it. People Are the Easiest Entry Point An attacker doesn’t need advanced tools if they can simply: Once a human opens the door, the system behaves exactly as designed. No hacking required. Just manipulation. Social Engineering Is About Psychology, Not Technology Social engineering works because it speaks to emotions, not logic. Messages are crafted to sound: When emotions rise, verification drops. This is why so many successful attacks involve phishing emails, fake support calls, job offers, or warnings about account problems. The technology isn’t failing it is the human moment that is being exploited. Why Awareness Is the Real Defense Security tools matter, but they can’t replace awareness. Cybersecurity depends on people knowing when to pause, when to question urgency, and when to verify through another channel. This is why cybersecurity is not just a technical field.It’s a human one. Final Thought If attackers can control your emotions,they can control your actions. And once they control your actions,they don’t need to hack any system at all. The strongest defense isn’t fear it’s awareness, patience, and understanding how the mind is used in attacks. Remember to ‘Never Trust, Always Verify’
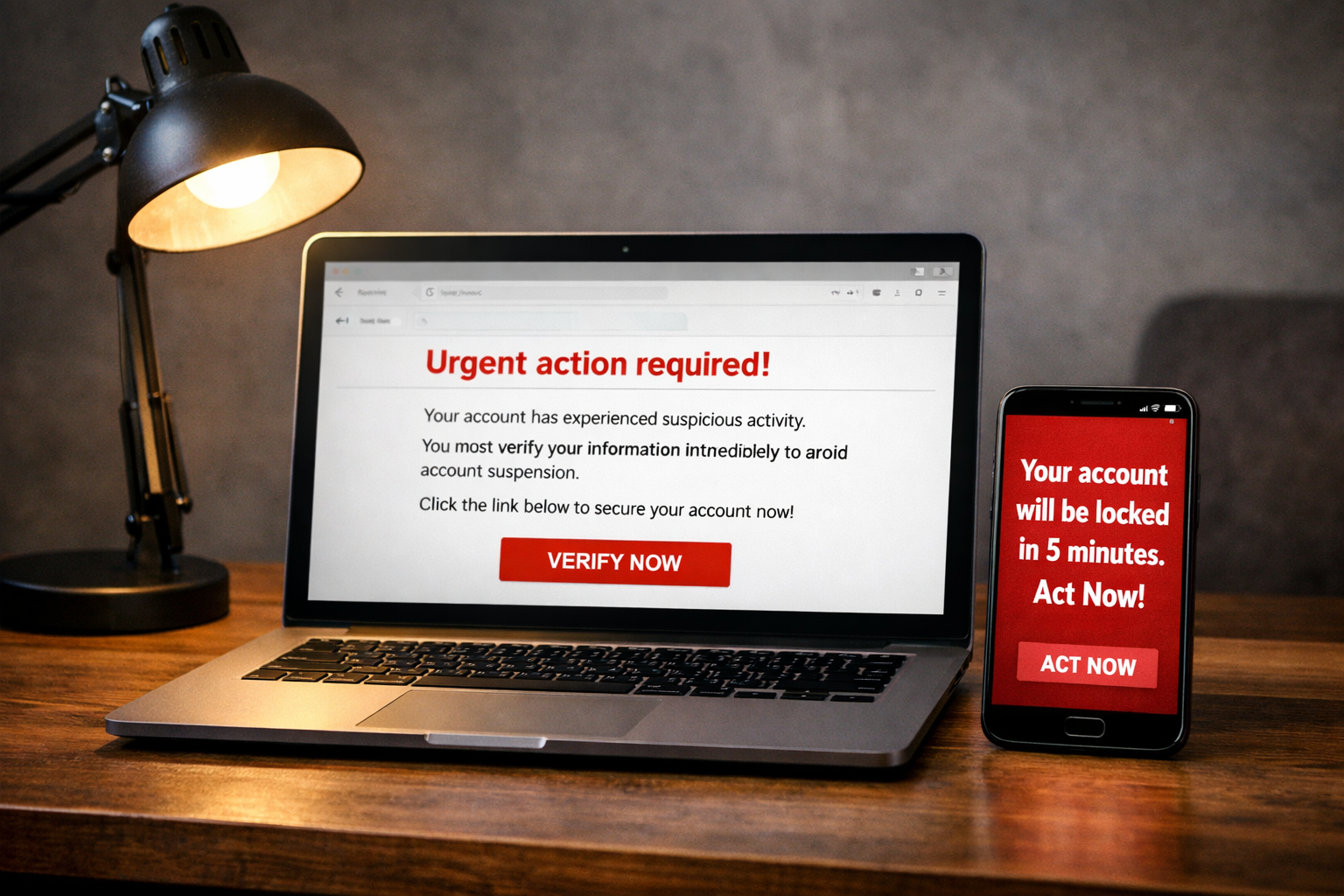
The Most Dangerous Word In Cybersecurity Is ‘Urgent’
In cybersecurity, many attacks don’t start with hacking tools or technical tricks. They start with one word: Urgent. That word has caused more people to lose accounts, money, and data than most viruses or malware. Why? Because the moment something feels urgent, people stop thinking clearly. Attackers know this very well. Why Attackers Use the Word “Urgent” When something feels urgent, fear kicks in. You feel pressure to act fast so you don’t lose something important. Once fear takes over, logic goes quiet. That’s why attackers use messages like: The goal is simple:make you panic so you act without thinking. Urgency Makes People Skip Checks When people feel rushed, they don’t verify.They don’t double-check links.They don’t ask questions.They don’t slow down. They click. They respond. They approve access. And once that happens, the damage is already done. Most cyber incidents happen not because someone is careless, but because they felt pressured to act quickly. Good Security Slows You Down Strong security systems are designed to slow people down on purpose. That’s why important actions need: These steps are not there to annoy you.They are there to protect you when emotions are high. Urgent Does Not Always Mean Real Not everything urgent is true.Real companies give you time to verify.Real problems can be checked through official channels. Fake urgency falls apart when you pause and question it. The Real Skill Is Control Cybersecurity is not about acting fast.It is about acting wisely. When you slow down, you take back control.And when you take back control, most attacks fail. Final Thought If a message tells you to act immediately, pause.Take a breath.Verify first….. Never Trust, always verify! Want more like this?I write about human-centred cybersecurity, risk, and career transitions.
Why Slowing Down Is A Security Skill
In cybersecurity, speed is often praised. Fast detection. Fast response. Fast recovery. But there’s a quieter skill that prevents more incidents than most tools ever will: Slowing down. Many security incidents don’t happen because systems fail. They happen because humans move too fast. A rushed click. A hurried response. An emotional reaction to pressure. Attackers understand this deeply and they exploit it. They don’t need you to think.They need you to react. Urgency Is Designed to Create Fear Urgency is not accidental. It is deliberate. When urgency enters a message, it creates fear. And once fear takes over, rational thinking steps aside. At that point, the attacker doesn’t need access to your system they already have access to your mind. This is how control is gained. Reflect for a moment on situations in your life where it felt like if you didn’t act immediately, something terrible would happen. A missed opportunity. A lost account. A looming consequence. Now ask yourself:How many times did you fail to meet that urgency… and heaven did not fall? That realisation alone is powerful. Social Engineering Is a Mind Game Social engineering does not rely on technology. It relies on psychology. It plays on: Once emotion takes the lead, logic struggles to catch up. That’s why slowing down matters. Slowing Down Restores Control Slowing down breaks the spell. It gives you space to ask: Most malicious requests collapse under simple scrutiny. From a security perspective, slowing down reduces risk. It increases verification, limits impulsive decisions, and prevents attackers from steering your actions. Patience Is a Security Virtue In cybersecurity, patience is not weakness it is strength. Mature security systems are designed to slow people down on purpose: confirmation steps, approvals, reviews, and delays. These controls exist because humans are emotional, and emotions can be exploited. Slowing down protects not just systems, but people. Final Thought Social engineering is a mind game.Security is knowing when not to play. Slow down.Question urgency.Trust verification over fear. And sometimes you need toslow down and smell the cookie. Because control begins the moment you pause. Want more like this?I write about human-centred cybersecurity, risk, and career transitions.
Personal Digital Hygiene Tips for the Holiday Season
The holiday season is a time for joy, travel, reconnection, and celebration. It’s also a season when many of let our guard down online and offline. Unfortunately, attackers know this too. When we are distracted, excited, or eager to share good moments, our digital hygiene often slips. That is why being intentional during this season matters more than ever. Think of digital hygiene the same way you think of personal hygiene:small, consistent habits that quietly protect you. 1. Be Mindful of What You Share Especially During Travel To my fellow African brothers and sisters travelling home to celebrate:resist the urge to show off. The “I have arrived” mentality of posting locations, arrivals, gifts, or lifestyle updates in real time can expose you and your loved ones to unnecessary risk. Protect yourself and your family by: Privacy is protection. Not everything needs an audience. 2. Keep Certain Things Private for Your Own Safety Not everyone watching your posts has good intentions.Some people are observing quietly, connecting dots, and gathering context. What feels like harmless celebration can become useful information to someone with the wrong motives. Digital hygiene means knowing that: 3. Be Extra Careful with Holiday Messages and “Opportunities” During the festive season, messages increase giveaways, offers, collaborations, job promises, and quick favors. Slow down before responding. You don’t owe strangers access to your time or your trust. 4. Young Ladies: Be Intentional About Online Relationships This part matters. Please don’t fall for “he said he lives abroad” as proof of legitimacy.Photos can be edited. Stories can be curated. Lifestyles can be staged. It is incredibly easy to make life look a certain way online. And the truth is simple:you don’t need someone abroad to validate your worth or your future. If you’re earning a decent salary, building your life, and growing you can travel abroad by yourself. You don’t need illusions sold through messages and filtered photos. Digital hygiene also means emotional hygiene. 5. Use Strong Passwords and Enable 2FA Avoid passwords linked to anything visible on your social media names, dates, locations, hobbies. Make sure Two-Factor Authentication (2FA) is turned on for: That extra step protects you when emotions or distractions creep in. 6. Be Careful with Direct Messages Scammers love the holidays because people are more open and less guarded. If a message feels: Pause and Verify. 7. Awareness Is the Real Gift Digital hygiene is not about fear.It is about intentional living online and offline. Understanding that: …is one of the strongest forms of protection you can give yourself and your family. Final Thought Enjoy the holidays.Celebrate fully.Reconnect with loved ones. Just remember:what you keep private today can protect you tomorrow. Security starts with awareness and awareness is always in season. Merry Christmas!