In March 2026, Navia Benefit Solutions confirmed a major data breach affecting approximately 2.7 million individuals. At first glance, this might seem like just another cybersecurity incident. But when you look closer, this breach is a powerful example of how failures in risk management, governance, and oversight can lead to real-world consequences. Let’s break it down in a way that helps you understand how cybersecurity works beyond just tools and technical jargon. What Happened? Navia, a company that manages employee benefits for over 10,000 employers, holds a large amount of sensitive data, including: According to the report, attackers gained unauthorised access through a vulnerability in an API used by the organisation. This incident is best understood as a third-party supply chain attack. This means the attackers did not directly break into the core system first. Instead, they exploited a weakness in a connected system or interface, allowing them to access sensitive data indirectly. Another important detail is that the attackers had read-only access, which allowed them to move quietly within the system without immediately triggering alarms. Understanding the Risk Behind the Breach To understand what really happened, we need to apply a core concept in cybersecurity: Asset + Threat + Vulnerability = Risk 🔹 Asset The sensitive data Navia was responsible for protecting, including personal and health-related information of millions of users. 🔹 Vulnerability A weakness in the API, likely due to insufficient security controls, validation, or monitoring. 🔹 Threat A malicious third party exploiting that weakness to gain unauthorized access. The Risk Realized Because all three elements existed together, the result was a large-scale data exposure affecting millions of individuals. Where Governance and GRC Failed This incident is not just a technical issue it is a clear example of gaps in GRC (Governance, Risk, and Compliance). First, there is the question of risk identification. Was this vulnerability known but not prioritised? If so, that reflects a failure in risk management processes. Second, there is the issue of oversight. Organisations that handle sensitive data at this scale must ensure continuous monitoring, strong access controls, and regular security assessments, especially for connected systems and third-party integrations. Third, detection was delayed. Because the attackers had read-only access, they were able to remain undetected for longer. This suggests weaknesses in monitoring, logging, and alerting systems. The Real Risk After the Breach Even though direct financial data may not have been accessed, the exposed information still creates serious risks. This includes: This highlights an important lesson: The impact of a breach is not only what is accessed, but how that information can be used later. What This Teaches About GRC This case clearly shows why GRC is critical in modern organisations. Governance ensures that responsibilities, policies, and controls are clearly defined. Risk management focuses on identifying vulnerabilities before they are exploited and prioritising what needs to be addressed. Compliance ensures that organizations meet legal and regulatory requirements when handling sensitive data. When any of these areas are weak, incidents like this become more likely. Key Lessons for Beginners in Cybersecurity If you are planning to study cybersecurity or transition into this field, this case teaches you something very important. Cybersecurity is not just about tools or technical skills. It is about understanding risk, making decisions, and protecting what matters. Every system has vulnerabilities. The goal is not to eliminate all risk, but to manage it effectively. And most importantly: Cybersecurity starts with risk management. If you don’t understand risk, you won’t understand what you are protecting or why it matters. On a final note… The Navia breach is not just a news story. It is a real-world example of what happens when valuable assets, existing vulnerabilities, and active threats come together. That combination is what creates risk. And that is why risk management sits at the heart of cybersecurity, GRC, and data protection.
What Are Cybersecurity Risks? Simple Explanation + Examples for Beginners (2026)
If you are new to cybersecurity, you have probably heard the term “cybersecurity risks” thrown around a lot. But what does it actually mean? Let’s break it down in the simplest way possible. What Is a Cybersecurity Risk? A cybersecurity risk is: The possibility that a threat can exploit a vulnerability in an asset and cause harm. To truly understand this, you need to know three key things: So in simple terms: Asset + Threat + Vulnerability = Risk If there is no asset, there is nothing to protect so there is no risk. Think of It Like This Imagine your house: The chance that the thief enters your house through the unlocked door = Risk Common Types of Cybersecurity Risks (With Examples) Let’s look at real-life examples so it becomes clear. 1. Weak Passwords Asset: Your email or bank accountVulnerability: Simple password like 123456Threat: Hackers using password-cracking tools Risk: Your account gets accessed and sensitive information is stolen 2. Phishing Attacks Asset: Your personal or financial informationVulnerability: Trusting fake emails or linksThreat: Cybercriminals pretending to be legitimate organizations Risk: You unknowingly give away your login details 3. Malware (Viruses) Asset: Your computer or smartphoneVulnerability: Downloading from untrusted sourcesThreat: Malicious software Risk: Your data is stolen or your system is damaged 4. Third-Party (Vendor) Risk Asset: Company or customer dataVulnerability: Weak security in a vendor’s systemThreat: Attackers targeting that vendor Risk: Your data is exposed through another company 5. Unsecured Data Asset: Sensitive files (customer data, personal records)Vulnerability: No encryption or access controlThreat: Unauthorized users or attackers Risk: Anyone can access or leak the data Why Cybersecurity Risks Matter Cybersecurity risks are not just technical problems they affect real lives and businesses. They can lead to: For individuals, this could mean identity theft.For businesses, it could mean losing millions. How Can You Reduce Cybersecurity Risks? You don’t need to be a tech expert to start protecting yourself. Here are simple steps you can take: On a final note Cybersecurity risks are everywhere but they become easier to understand when you break them down. Always remember: No asset = no riskRisk exists when a threat can exploit a vulnerability in something valuable And if you are planning to study or transition into cybersecurity, this is something you must understand early: Cybersecurity is not just about tools or hacking it starts with risk management. If you don’t understand risk, you won’t understand what you’re trying to protect or why it matters. That’s why risk management is the foundation of careers in GRC, data privacy, and cybersecurity.
The First Four Hours of a Cyber Incident: Why Human Decisions Matter Most
At 09:00 on a Monday morning, the security dashboard lit up with alerts. Unusual network activity.Multiple authentication failures.Files suddenly becoming inaccessible. Within minutes, the IT team realised something serious was happening. Systems that had worked perfectly the night before were now behaving unpredictably. Employees began reporting that shared folders would not open. By 09:40, the first encrypted file appeared. What had started as a strange technical glitch had now become a cybersecurity incident. And the most important decisions had to be made quickly. Because in cybersecurity, the first four hours often determine whether an incident becomes a contained disruption or a full-scale crisis. Why the Early Hours Matter So Much When people imagine cyberattacks, they often picture hackers typing lines of code in dark rooms. In reality, many attacks unfold quietly over time. Attackers may spend days or weeks inside a network before they are detected. But once an incident becomes visible, the organisation enters a critical window of response. These early hours are when teams must decide: Every one of these decisions carries risk. Shutting down systems too early may disrupt operations unnecessarily. Waiting too long may allow attackers to spread further across the network. In those first few hours, organisations are not just responding to technology. They are responding to uncertainty. Technology Detects Incidents. Humans Decide What Happens Next. Modern cybersecurity tools are incredibly sophisticated. Security monitoring systems can detect anomalies across millions of network events. Artificial intelligence can flag suspicious behaviour faster than any human analyst. But technology alone does not manage a cyber crisis. People do. When an incident begins, someone must decide: These decisions rarely happen in calm conditions. They happen while teams are still trying to understand what is actually going on. The pressure can be intense. Senior leadership wants answers. Employees want reassurance. Customers expect stability. In these moments, the organisation is not just defending its network. It is defending its ability to think clearly under pressure. Communication Becomes the Real Battlefield One of the most overlooked risks during cyber incidents is communication failure. When teams operate in silos, confusion spreads quickly. IT teams may focus on technical containment while business leaders worry about operational disruption. Legal teams may be considering regulatory obligations while communications teams prepare external statements. Without clear coordination, even skilled teams can end up working against each other. This is why mature organisations treat cybersecurity incidents as cross-departmental crises, not purely technical events. Security teams must collaborate with: The speed and clarity of communication often determine whether the organisation regains control quickly or loses valuable time. In aviation, this principle is deeply understood. When something goes wrong in the cockpit, pilots rely on structured communication protocols to coordinate their response. Clear language, defined roles, and shared situational awareness prevent confusion during high-pressure moments. Cybersecurity teams increasingly need the same kind of discipline. The Hidden Risk: Decision Paralysis During the early hours of a cyber incident, one of the greatest dangers is not making the wrong decision. It is making no decision at all. Teams may hesitate because they lack complete information. They may fear shutting down critical systems unnecessarily. They may hope the situation resolves itself. But attackers rarely wait. While teams debate their next steps, malicious software can spread across networks, escalate privileges, and exfiltrate data. The organisations that recover fastest are not always the ones with the best technology. They are the ones with the clearest decision frameworks. Prepared organisations run incident simulations. They practice response scenarios. They define leadership roles before a crisis ever begins. When incidents occur, they are ready to act. Governance Is the Real Foundation of Incident Response Strong incident response is not built in the moment of crisis. It is built long before the incident begins. Organisations that respond effectively usually have several governance elements already in place: These structures provide guidance when uncertainty appears. Without them, teams are forced to improvise under pressure. And improvisation during a cyber crisis can be dangerous. The Human Side of Cybersecurity Many discussions about cybersecurity focus on tools, technologies, and vulnerabilities. But behind every cyber incident is a series of human decisions. Someone decides whether a suspicious alert is investigated.Someone decides whether a system is isolated from the network.Someone decides how the organisation communicates with employees and customers. Cybersecurity is not only about protecting systems. It is about enabling people to respond intelligently when systems fail. The organisations that handle incidents best are not those that never experience attacks. They are the ones that have built cultures of preparedness, accountability, and coordinated decision-making. Because when a cyber incident begins, technology may raise the alarm. But it is human judgement that determines the outcome.
When a Vendor Gets Hacked: A Ransomware Incident That Shut Down Payroll Systems
When Payroll Stops: Lessons From a Ransomware Incident That Started With a Trusted Vendor At 08:15 on a Monday morning, the finance team noticed something strange. The payroll system would not load. At first, it looked like a simple outage. Systems fail sometimes. Servers reboot. IT fixes it. But within minutes, it became clear this was not a routine problem. Files across the finance server had been renamed. Critical payroll data was inaccessible. A message appeared on the screen demanding payment to restore access. What had started as a small technical issue was now a Severity 1 cybersecurity incident. And the most unsettling discovery came next. The attack did not begin inside the organisation.It started with a trusted third-party vendor. The Invisible Door Attackers Walk Through The organisation relied on a financial software provider to manage payroll processing and financial reporting. The system had been trusted for years. It handled sensitive employee data and critical operational functions. But trust in technology can create blind spots. Unknown to the company, the vendor’s software supply chain had been compromised. Attackers exploited a vulnerability in the vendor’s update mechanism, embedding ransomware into a routine software update. Once installed inside the organisation’s environment, the malicious code began spreading silently. By the time employees noticed something was wrong, the ransomware had already encrypted multiple systems. The attackers never had to break down the company’s front door. They simply walked through a door that had already been opened by a trusted supplier. This kind of incident is becoming increasingly common in modern cybersecurity. Supply-chain attacks have shown that organisations are often only as secure as the vendors they depend on. The breach itself was technical. But the underlying problem was governance. The First Four Hours That Decide Everything When a cyber incident begins, the first few hours often determine whether the damage spreads or is contained. In this case, the organisation activated its incident response process immediately. The response team initiated several critical actions: Communication became just as important as technical containment. Executives needed to understand the potential business impact. Finance teams needed clarity on payroll delays. Legal teams needed to evaluate regulatory obligations. Cybersecurity incidents rarely affect only one department. They ripple across the entire organisation. During these early hours, leadership decisions matter just as much as technical expertise. Poor communication can amplify confusion. Delayed decisions can allow attacks to spread further. In crisis moments, cybersecurity becomes less about technology and more about people coordinating under pressure. When Cybersecurity Becomes a Business Crisis The ransomware attack did more than disrupt IT systems. It threatened core business operations. Payroll systems store some of the most sensitive data in any organisation: employee identities, salaries, bank details, tax records. If compromised, the consequences can extend far beyond operational disruption. The organisation now faced multiple risks at once. Financial operations were interrupted. Employee payments were uncertain. Sensitive data exposure was a real possibility. And if personal data had been compromised, the organisation might be required to notify regulators under the General Data Protection Regulation, which requires organisations to report certain data breaches within strict timeframes. What started as a ransomware attack had quickly evolved into a potential regulatory and reputational crisis. This is why cybersecurity leaders increasingly emphasise a simple truth: Cybersecurity incidents are rarely just IT problems. They are business continuity problems. The Vendor Risk Most Organisations Underestimate The most important lesson from this incident was not about ransomware. It was about third-party risk. Modern organisations rely on dozens, sometimes hundreds, of external software providers. Each vendor introduces a potential entry point into the organisation’s systems. Yet vendor security often receives far less scrutiny than internal infrastructure. Questions that should be asked frequently are often overlooked: How secure are the vendor’s update mechanisms? How are software patches verified before installation? What monitoring exists for abnormal behaviour after system updates? Without strong governance around vendor risk management, organisations may unknowingly inherit vulnerabilities from the partners they trust the most. Incidents like this demonstrate that cybersecurity is no longer confined within organisational boundaries.Security now extends across entire digital supply chains. A Lesson From Aviation Safety This incident reminded me of something deeply embedded in aviation safety culture. In aviation, incidents are rarely blamed on a single failure. Investigators look for systemic causes. Was there a process gap? Was communication unclear? Was a critical risk underestimated? Cybersecurity incidents often follow the same pattern. The ransomware itself may have been the trigger, but the real issue lies deeper: governance, oversight, and risk awareness. Just as aviation learned that safety requires coordination across pilots, maintenance teams, regulators, and manufacturers, cybersecurity now requires coordination across organisations, vendors, and technology providers. Security is not simply about building stronger technical defenses. It is about building stronger systems of accountability. The Real Question Organisations Should Ask When organisations analyse cyber incidents, the focus often remains on the attacker. How did they gain access? What vulnerability did they exploit? How can we block it next time? Those are important questions. But a more powerful question may be this: What assumptions allowed this incident to happen? In this case, the assumption was trust. Trust in a vendor. Trust in software updates. Trust that someone else had already handled the risk. Cybersecurity incidents often expose the invisible assumptions embedded in organisational systems. And when those assumptions break, the consequences can ripple across an entire business. The Future of Cybersecurity Is Human-Centered As cyber threats grow more complex, one lesson is becoming clearer. Technology alone cannot solve cybersecurity. Behind every vulnerability is a decision. Behind every incident is a process. Behind every breach is a system of human choices. The future of cybersecurity will not only depend on better tools or stronger encryption. It will depend on organisations learning to see security as a shared responsibility across people, processes, and partners. Because sometimes the most dangerous vulnerability is not hidden in code. It is hidden in the systems we trust without questioning.
Why Many Companies Don’t Know Their Most Critical Cyber Risks
Why Many Companies Don’t Know Their Most Critical Cyber Risks On Monday morning, the security team gathered for their weekly risk meeting. A spreadsheet appeared on the screen. It was the company’s cyber risk register. It had everything. Dozens of risks. Columns for likelihood and impact. Risk scores in red, orange, and yellow. At first glance, it looked impressive. But something was wrong. When the Chief Technology Officer asked a simple question, the room became quiet. “Which of these risks could stop our business tomorrow?” No one answered immediately. The security analyst began scrolling through the list. There were many risks labeled “High”. Unpatched servers. Weak passwords. Outdated software. Cloud configuration issues. Everything looked important. But that was the problem. When everything is marked as high risk, nothing truly stands out. The meeting ended without a clear answer. This situation is more common than many organisations realise. Many companies do not have full visibility of their digital environment. New systems are added quickly. Cloud services are created by different teams. Applications are deployed without security teams always knowing about them. Over time, organisations lose track of what they actually need to protect. If a company does not clearly understand its systems, it becomes very difficult to understand its real cyber risks. Another common problem is that security teams focus heavily on technical vulnerabilities instead of business impact. A vulnerability scanner may report hundreds of issues. But not every vulnerability creates the same level of risk. For example, a vulnerability in an internal testing server may cause inconvenience, but a vulnerability in a payment processing system could stop revenue completely. Technically, both issues may appear severe. But from a business perspective, they are very different risks. When organisations fail to connect cybersecurity issues to business operations, it becomes difficult to identify what truly matters. In many organisations, the risk register also becomes a documentation exercise. Risks are listed, scores are assigned, and review meetings are scheduled. But the register is not actively used to guide decisions. Instead of helping leaders understand the most important risks, it becomes just another document that grows longer over time. Another issue is unclear ownership. Cyber risks often sit between different teams. IT teams manage systems. Security teams identify vulnerabilities. Business units depend on those systems to operate. But when a risk appears, it is not always clear who is responsible for fixing it. Without clear ownership, risks remain unresolved. Eventually organisations struggle to answer a very simple question: what cyber risk could hurt the business the most? Instead of focusing on a few critical risks, teams try to manage everything at once. Attention becomes spread too thin. Organisations that manage cyber risk well take a different approach. They focus on understanding how technology supports the business. They identify which systems are critical for operations. They connect cyber risks directly to financial impact, operational disruption, and customer trust. Most importantly, they ensure that every major risk has a clear owner. Because cybersecurity is not only about protecting systems. It is about protecting the business itself.
Why Risk Registers Fail in Organisations (And How to Fix Them)
One Monday morning, the security team gathered for their regular risk review meeting. The risk register was open on the screen. It was a long spreadsheet filled with risks, scores, and notes about possible controls. Everything looked organised. But after some time, the discussion slowed down. Some risks had been on the list for months. Many of them were marked as “High.” A few risks did not even have a clear owner. The team realised something important. The risk register existed, but it was not really helping them decide what to do. This situation happens in many organisations. Risk registers are created with good intentions, but over time they stop being useful. One common reason is that the risk register becomes just another document. Teams update it because governance processes require it or because auditors expect to see it. Instead of helping people manage risk, the register slowly becomes a record of problems that no one is actively solving. Another problem is that too many risks are marked as “High.” When teams score risks, they often want to be cautious, so they rate many issues as high priority. At first this seems responsible, but when almost every risk is labelled “High,” it becomes difficult to know which ones truly need urgent attention. When everything looks critical, nothing clearly stands out. Risk registers also fail when risks do not have clear owners. A risk might say that outdated systems could create security vulnerabilities. That sounds serious, but who is responsible for fixing it? If there is no clear owner, the risk stays in the register but no action is taken. Sometimes the way risks are described also causes problems. Many risks are written in technical language that business leaders may not fully understand. For example, a risk might mention outdated encryption protocols or system vulnerabilities. While these are technical issues, they do not clearly explain what could happen to the business. When risks are connected to real outcomes like financial loss, regulatory penalties, service disruption, or customer impact, leaders can better understand why they matter. In some organisations, the risk register is updated regularly but rarely used to guide decisions. The document exists, and teams review it occasionally, but it does not influence how security resources are prioritised or how risks are addressed. When that happens, the register becomes part of a process rather than a tool for action. A good risk register should help organisations focus on the risks that matter most. It should make it easier to see which risks require immediate attention, which risks need mitigation, and which ones the business may decide to accept. For a risk register to work properly, risks need clear scoring criteria, clear ownership, and regular review. Most importantly, the risks should be linked to real business consequences. When these elements are in place, the risk register becomes more than just a list of problems. It becomes a tool that helps organisations make better decisions about managing cyber risk.
How Women With No Tech Background Are Breaking Into Cybersecurity in 2026
Every year, the cybersecurity industry faces a growing problem: there are millions of unfilled jobs worldwide, yet many talented women still believe tech is “not for them.” For a long time, cybersecurity was seen as a field reserved for programmers and computer science graduates. But in 2026, that narrative is changing fast. More women from non-technical backgrounds teachers, nurses, marketers, customer service agents, and even flight attendants are successfully transitioning into cybersecurity careers. The truth is simple: cybersecurity needs diverse thinkers, not just technical experts. Many of the most valuable skills in security today come from backgrounds outside traditional tech. If you’ve ever thought about switching careers but felt intimidated by the tech barrier, this might surprise you, you may already have skills the cybersecurity industry desperately needs. Why Cybersecurity Is Attracting More Women Cybersecurity has become one of the most attractive career paths globally, and women are increasingly stepping into the field for several reasons. First, the demand for cybersecurity professionals is exploding. Organisations across finance, healthcare, aviation, government, and technology need experts to protect their systems from cyber threats. Second, cybersecurity offers flexible career paths. Unlike many tech roles, you don’t necessarily need a computer science degree to get started. Many professionals enter the field through certifications, training programs, and practical experience Third, cybersecurity careers often provide competitive salaries and global opportunities, making it appealing for women looking for financial independence and career growth. Most importantly, companies are beginning to realize that diverse teams build stronger security systems. Different perspectives help organisations identify risks that homogeneous teams might overlook. The Biggest Myth: “You Must Be a Tech Genius” One of the biggest misconceptions about cybersecurity is that you must know how to code or have an advanced technical background. While technical skills are helpful, many cybersecurity roles focus on risk management, policy development, compliance, and governance rather than deep programming. For example, roles such as: often rely more on analytical thinking, communication, and problem-solving skills than heavy technical expertise. This is exactly why women from non-technical backgrounds are increasingly finding their place in cybersecurity. Transferable Skills Women Already Have Many women underestimate how valuable their existing skills are in cybersecurity. Here are some examples of transferable skills that translate well into security roles: Communication SkillsCybersecurity professionals must explain complex security issues to non-technical stakeholders. Strong communication is essential. Risk AwarenessMany roles involve identifying and assessing risks something professionals in finance, aviation, healthcare, and management already do. Attention to DetailCybersecurity requires noticing patterns, anomalies, and vulnerabilities. Precision and careful observation are critical skills. Problem SolvingSecurity teams constantly analyze problems and develop strategies to prevent cyber threats. These skills are often developed in careers that have nothing to do with technology. Why 2026 Is the Best Time to Enter Cybersecurity The cybersecurity industry is evolving rapidly, and organisations are prioritizing diversity and inclusion more than ever before. Governments, technology companies, and security organisations are actively investing in programs designed to bring more women into cybersecurity roles. In addition, remote work opportunities have opened the door for professionals around the world to join the global cybersecurity workforce. This shift means women no longer need traditional tech backgrounds to build successful careers in security. Final Thoughts Cybersecurity is no longer an exclusive club for computer science graduates. It has become a field where problem solvers, communicators, and strategic thinkers can thrive. Women from non-technical backgrounds are proving that career reinvention is possible and often powerful. Breaking into cybersecurity may require learning new skills, gaining certifications, and building experience, but the opportunities are enormous for those willing to take the first step. In 2026, the question is no longer whether women can succeed in cybersecurity. The real question is how many more women will take the leap.
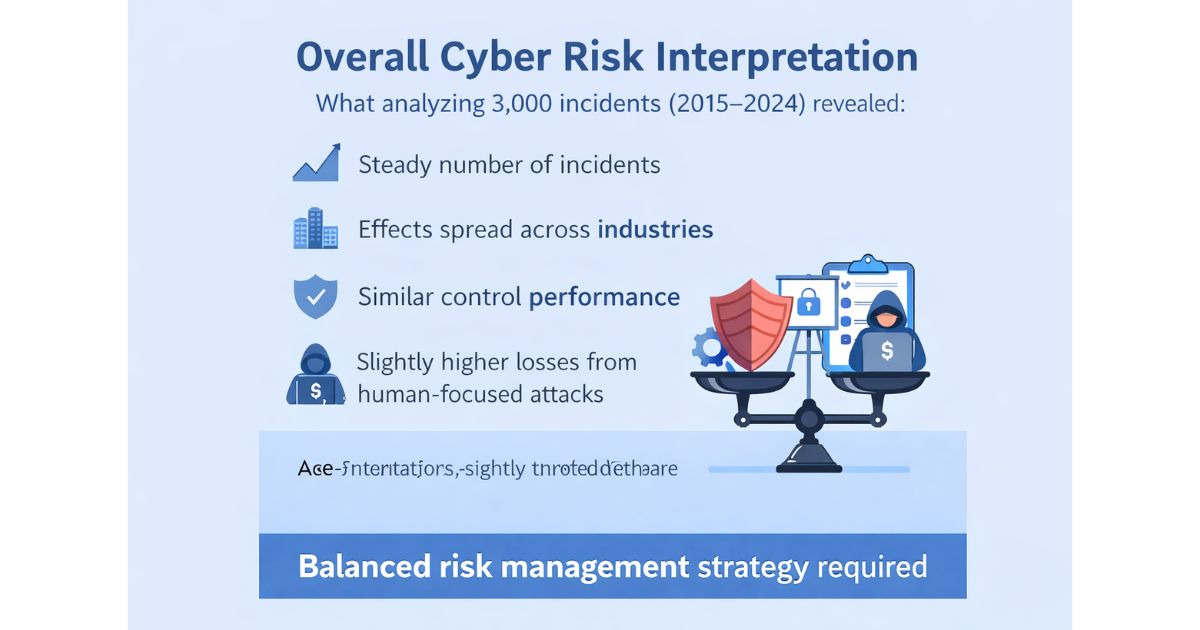
What 3,000 Cybersecurity Incidents Reveal About Risk (2015–2024)
Cyber risk is often discussed in headlines rising attacks, record-breaking breaches, increasing losses. But what does the data actually say? To explore this, I analyzed 3,000 cybersecurity incidents across multiple industries between 2015 and 2024 using Python (Pandas and Matplotlib). The objective was to understand patterns in financial impact, sector exposure, and control effectiveness from a governance and risk perspective. Are Attacks Increasing? Interestingly, incident frequency remained relatively stable across the 10-year period. While there were natural fluctuations year to year, the dataset does not show sustained growth in attack volume. From a risk management standpoint, this suggests steady exposure rather than escalating frequency — at least within this dataset. Which Industries Are Most Affected? Financial losses were broadly distributed across sectors. Although IT recorded the highest total loss, the difference between industries was not dramatic. Banking, Government, Healthcare, Retail, and Telecommunications all showed comparable exposure levels. This indicates that cyber risk is systemic rather than concentrated in one high-risk sector. It is a cross-industry issue. Do Certain Controls Reduce Financial Impact? When comparing median financial losses across defense mechanisms, no single control dramatically reduced impact. Firewall-associated incidents showed slightly lower median loss, but the differences between controls were relatively small. This reinforces a key governance principle: layered security matters more than relying on one solution. Which Vulnerabilities Are Most Expensive? Social engineering incidents showed the highest median financial loss, closely followed by zero-day vulnerabilities. This highlights an important reality: Cyber risk is both technical and human. Organizations must invest not only in infrastructure and detection systems, but also in awareness, training, and behavioral risk management. Overall Risk Interpretation The data shows that: From a governance point of view, cyber risk is spread across sectors and comes from different sources. It is not caused by one single major threat. This means organizations need a balanced approach combining strong technical controls, user awareness, and clear oversight from leadership. The pictures are below If you are working in cyber risk or governance, I will be interested in your perspective: Are you seeing similar patterns in your sector? Write in the comments below The full Jupyter Notebook and supporting files are available on GitHub: https://github.com/Iyetunde/Cyber-risk-analysis-2015-2024
Why Most Cyber Risk Scores Are Wrong
Most cyber risk registers look structured. They have: On paper, it appears disciplined. But in practice, many of those scores are unreliable. Not because people are careless but because the scoring process itself is weak. The Illusion of Precision A risk rated: Likelihood: 4Impact: 5Risk Score: 20 Looks precise. But ask two simple questions: If those definitions are unclear, the score is only structured guesswork. Precision in format does not equal accuracy in assessment. Likelihood Is Often Misjudged In many organisations, likelihood is scored based on: But proper likelihood assessment should consider: Without structured criteria, likelihood becomes subjective. Two departments may score the same risk differently because they interpret probability differently. That creates inconsistency across the risk register. Impact Is Frequently Inflated Impact scoring is where distortion becomes obvious. Common patterns include: When too many risks are rated “High,” prioritisation collapses. If ten risks are critical, none of them truly are Impact scoring should be based on clear business consequences, such as: Without calibration, impact becomes emotional rather than analytical. If Controls Don’t Work, the Risk Score Is Misleading Another common issue is scoring inherent risk without properly assessing control effectiveness. Controls may exist on paper but: If control strength is overestimated, residual risk is underestimated. That creates false confidence. Mid-level analysts understand that control design and operating effectiveness matter just as much as the initial risk score. High-Risk Inflation Weakens Governance When too many risks are labelled as “High”: When everything is treated as critical, it becomes hard to see what truly needs action first. Good governance depends on clear differences between risks. Risk scoring should help organisations decide what to fix first not create confusion. But you ask why does it stop feeling urgent, is too many “High” not meant to make it more urgent? High” should trigger urgency. But here’s the problem, Urgency only works when it’s scarce. If When everything is urgent, nothing feels urgent. Why This Matters for Decision-Making Cyber risk scoring is not an academic exercise. It influences: If the scoring process is inconsistent, decisions built on those scores are also inconsistent. That is where governance begins to weaken. How to Improve Risk Scoring Without Overcomplicating It You do not need full quantitative modelling to improve accuracy. You need to; Consistency matters more than mathematical complexity. When scoring logic is transparent and defensible, risk registers become decision tools not reports that sits on the shelf. Final Thought Cyber risk scores are not wrong because people lack intelligence. They are wrong because scoring systems are often under-designed. A well-structured scoring framework forces clarity. And clarity is what enables confident risk decisions.
Risk Ownership in Tech: The Most Overlooked Governance Problem.
The risk was documented. It had a score.It had a description.It even had recommended controls. But no one owned it. Weeks passed.Then months. The risk didn’t disappear. It just became invisible.This is one of the most overlooked governance problems in tech companies:unclear risk ownership. The Illusion of “Someone Is Handling It” In many tech environments, risks are identified quickly. Security tools generate alerts.Engineers log vulnerabilities.Compliance teams update risk registers. Everything looks organised. But when you ask one simple question Who owns this risk?the room goes quiet. Sometimes the answer is: That is not ownership. That is diffusion of responsibility. Control Owner vs Risk Owner This is where confusion begins. A control owner manages a safeguard.For example: But a risk owner is different. A risk owner is accountable for the business impact if the risk materialises. That person: In many tech companies, this distinction is blurred. Controls exist. Ownership does not. Why This Happens in Tech Companies Tech organisations move fast. New features.New integrations.New markets. In this environment: When risk ownership is unclear: And default risk acceptance is rarely strategic. Risk Ownership Is a Leadership Function Here is the uncomfortable truth: Risk ownership is not a technical role. It is a business role. If a customer data breach would impact revenue, reputation, and regulatory standing, the risk owner should sit at a level that understands those consequences. Security teams identify and assess. But business leaders decide. When risk ownership stays inside security alone, governance becomes unbalanced. What Clear Risk Ownership Changes When ownership is clearly assigned: The risk register stops being a static document. It becomes a decision-making tool. That shift changes everything. The Hidden Cost of No Ownership Unowned risks create: But the biggest cost is strategic blindness. If leadership does not explicitly accept or reject risks, the organisation drifts. Drift is dangerous in tech. How Governance Fixes This Good GRC does not just track risks. It clarifies: Governance is not about adding layers. It is about removing ownership gaps. Why This Matters Now As tech companies scale, complexity increases. Without strong ownership structures: Risk ownership is not a spreadsheet column. It is an operating model. And without it, even the best risk scoring system cannot drive strategy. Clear ownership turns risk from a warning into a decision. And governance begins where accountability becomes explicit.